Tasks
1. Basic IP addressing are pre-configured in this scenario.
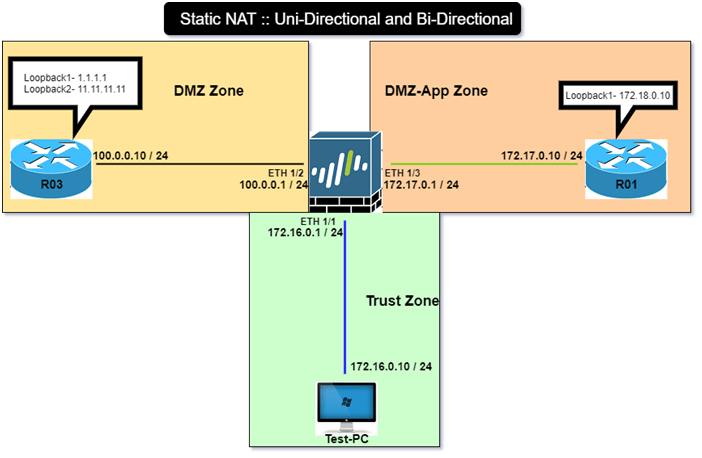
2. Configure Static NAT on Palo Alto from LAN to DMZ-App Zone.
3. Use below information:
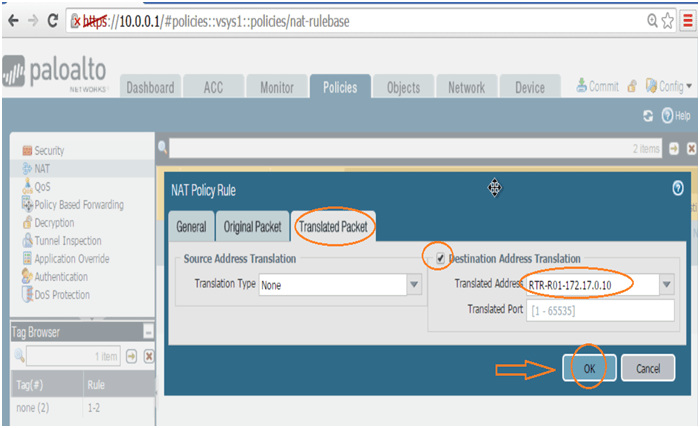
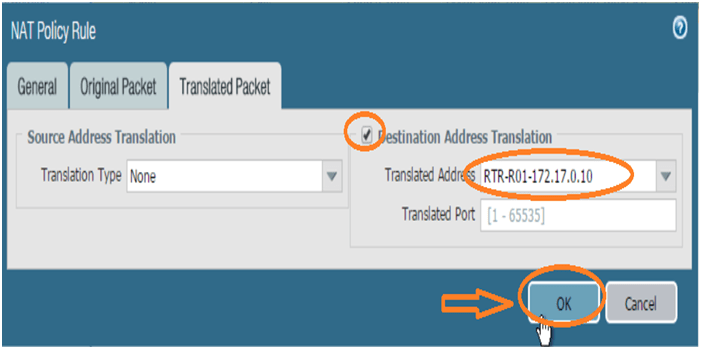
Case 1. Access R01 (on-DMZ-App zone) server with 100.0.1.10 (NATed IP) à 172.17.0.10 (Real-IP), this rule will be unidirectional in nature i.e. if anyone access it from any zone, it should be accessible via NATed IP, whereas when it wants to communicate with, DMZ and Trust zones, it should use its private IP address for communication.
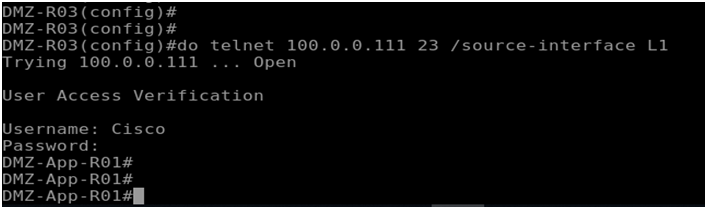
Case 2. Access R01 (on-DMZ-App zone) server with 100.0.0.111 (NATed IP) à 172.18.0.10 (L1-Real-IP), this rule will be Bidirectional in nature i.e. if anyone access it from any zone, it should be accessible via NATed IP, likewise if this wants to communicate with, DMZ and Trust zones, it should use it’s NATed IP address for communication.
4. Verify that implemented is unidirectional and bidirectional.
Explanation
NAT (Network address translation) was designed to address the depletion of the IPv4 address space. Since then Network address translation (NAT) is not only used to conserve available IP addresses, but also as a security feature to hide the real IP addresses of hosts, securely providing private LAN users access to the public addresses. NAT is also used to solve network design challenges, enabling networks with identical IP subnets communicate with each other.
NAT with PAN-OS
PAN-OS provides a mechanism for translating both the source IP addresses numbers and destination IP addresses numbers. PAN-OS uses rules to configure NAT. These rules are like a separate entity, and not configured as part of the allow/drop security rules. NAT rules are configured to match on:
Source and destination zone
Destination interface (optional)
Source and destination addresses
Service
The configurable fields in the NAT rule are as follow.
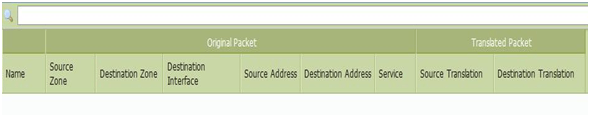
Multiple NAT rules can be configured on a PAN-OS device. NAT rules are evaluated top down like security rules. Once a packet matches a NAT rule, any other configured NAT rules are skipped for processing. So, more specific NAT rules must be at the top to the rule list.
When a packet matches the NAT rule the translated addresses are determined. It is very important to note that the IP address/port translation happens only when the packet egresses the firewall. Therefor the NAT rules and security rules always refer to the original IP addresses in the packet (i.e. the pre-NAT addresses).
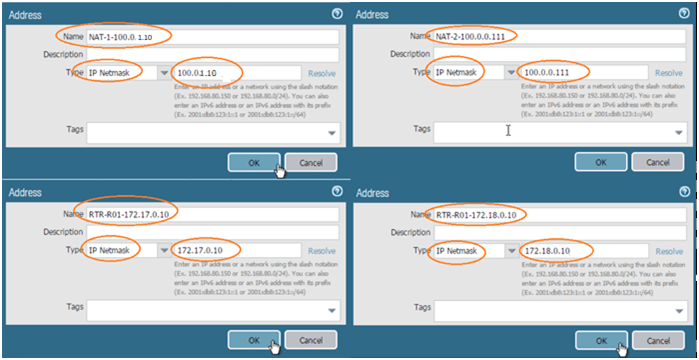
Address Pools: - In PAN-OS, the IP address (also commonly referred to as IP address pools) used for address translation is configured as an address object. The address object can be a host IP address, IP address range or IP subnet. Because these address objects are used both in the security policies and NAT rules, it is recommended to use names that identify these address objects specifically used as NAT address pools. For example, the names of address objects used in NAT rules begin with prefix “NAT-
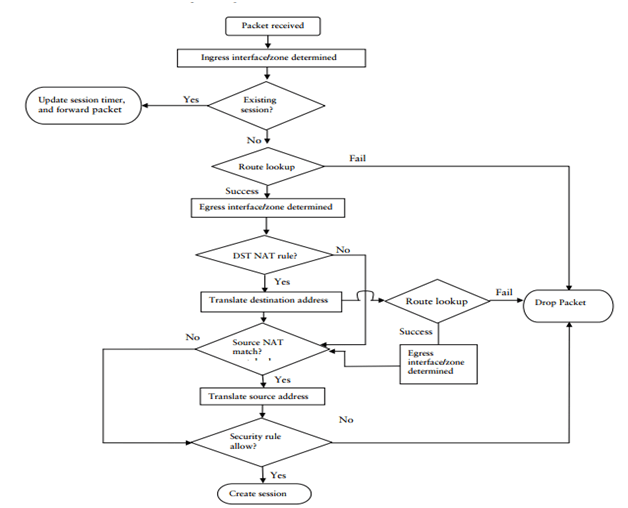
Proxy-ARP for NAT Pools: - The address pools are not bound to any interfaces. Address pool in the same subnet as the egress/ingress interface IP address, the firewall will respond to ARP requests received on that interface for the IP addresses implemented in the pool. If the address pool is not in the same subnet as the egress interface IP address, you should configure the necessary routes on the upstream devices in order to ensure the response traffic after address translation is routed back to the firewall.
Dynamic-ip
Static IP
IP address
IP subnet
Range of IP addresses
IP address
IP subnet, or
Range of IP addresses
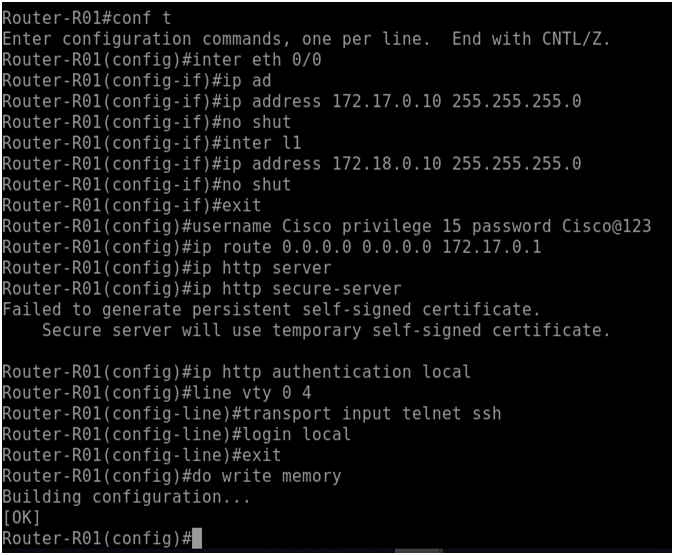
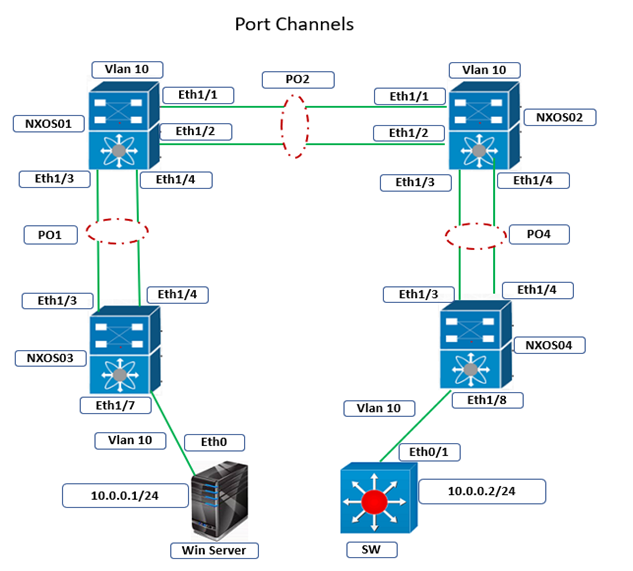
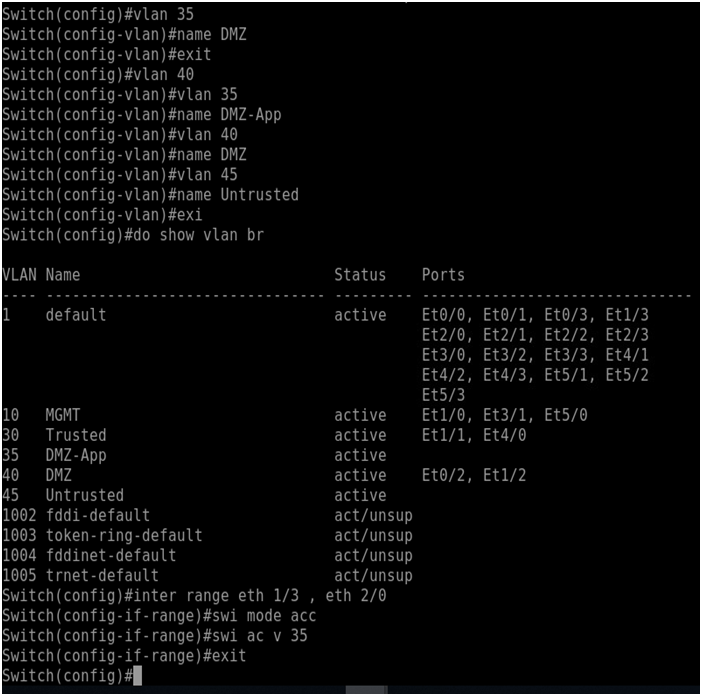
SWITCH-CONFIGURATION
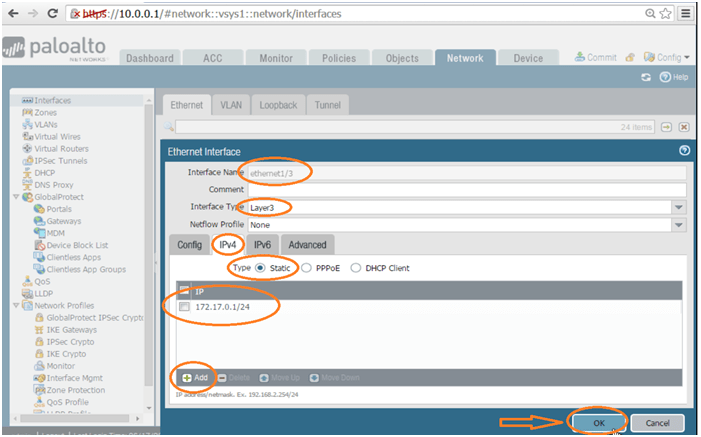
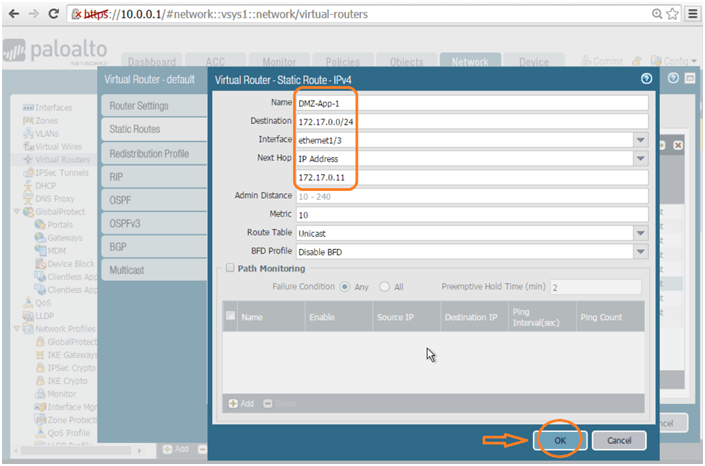
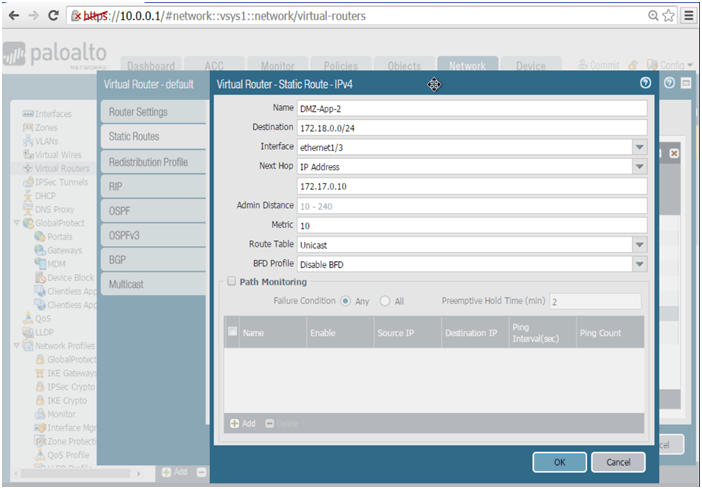
Configure VLAN on switch for communication between firewall eth 1/3 with router interfaces eth 2/0, eth 2/1.Below is the configuration:
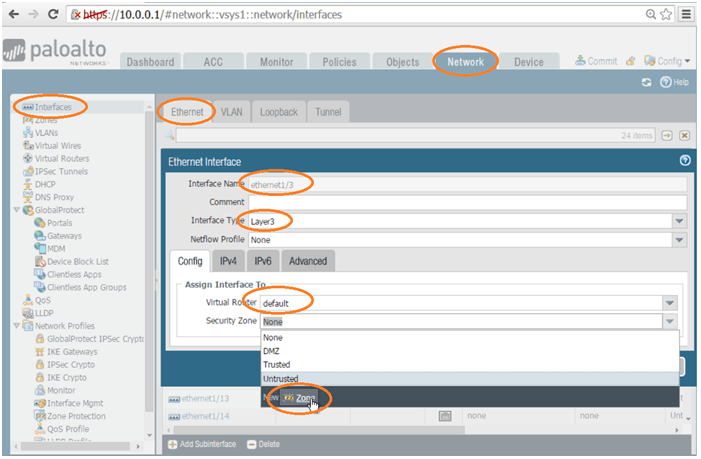
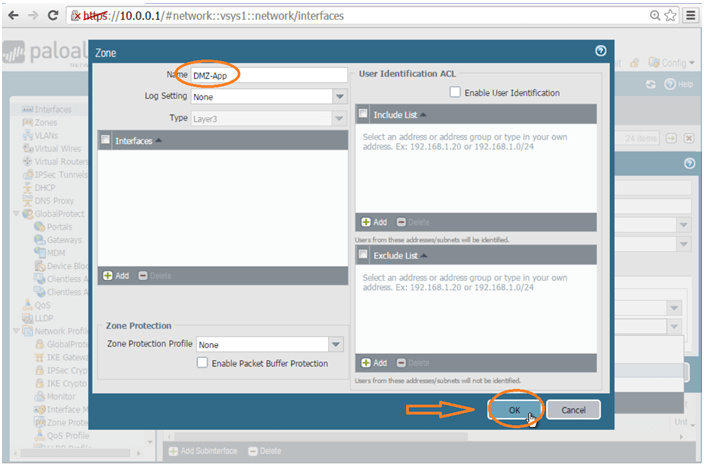
FIREWALL-CONFIGURATION
Object Tab >> Addresses >>>> Proceed with below objects highlighted in screenshots.
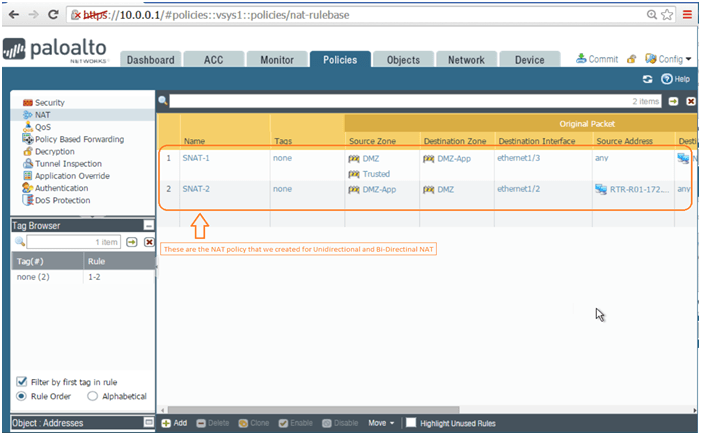
Now Let’s Create NAT Policy:
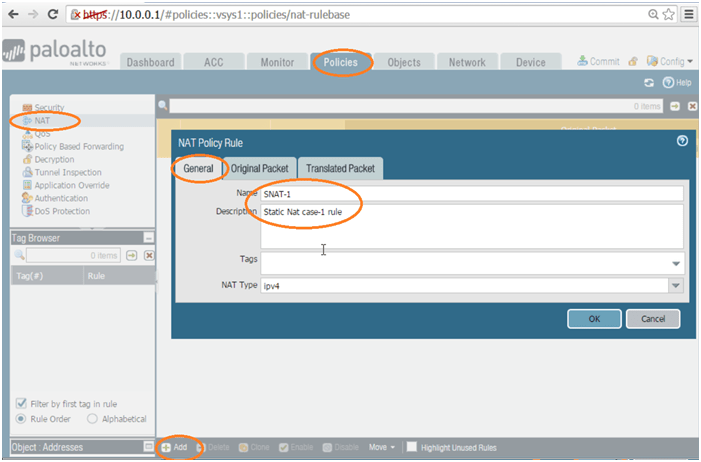
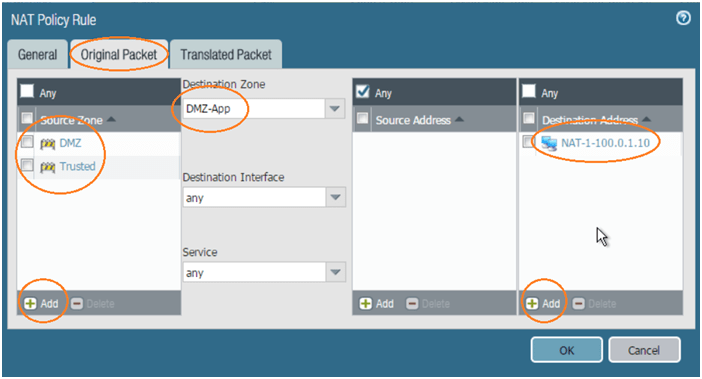
Above screenshot lists the network addressed required to complete case-1 only
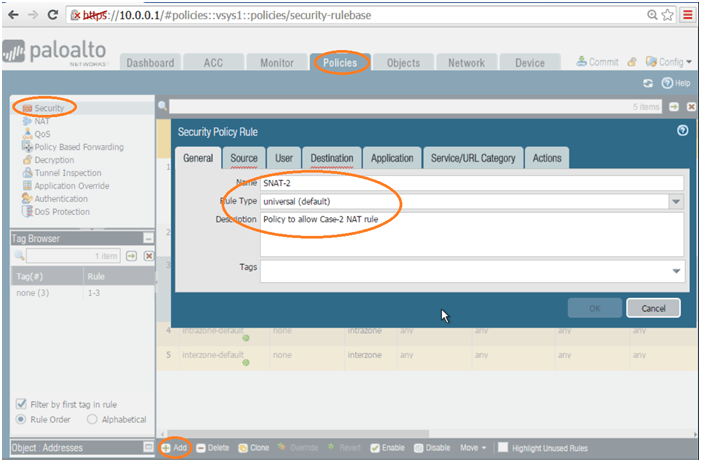
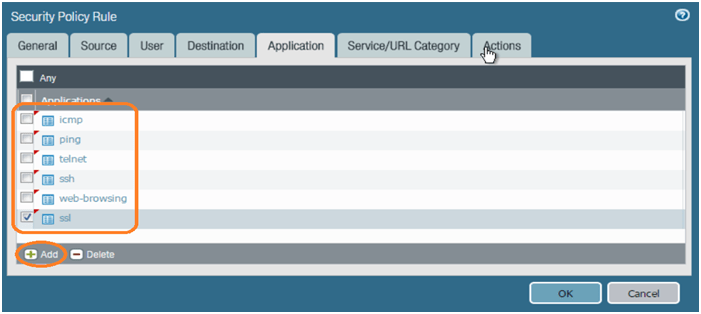
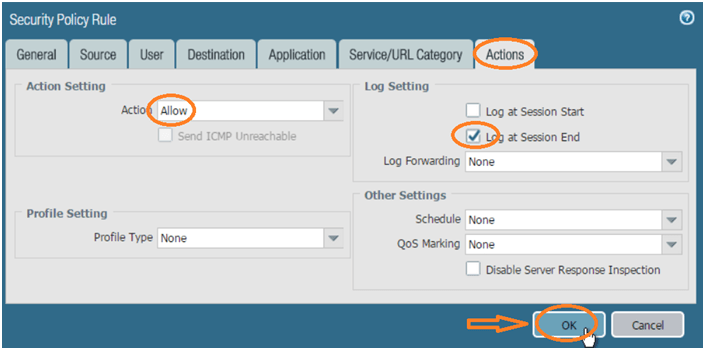
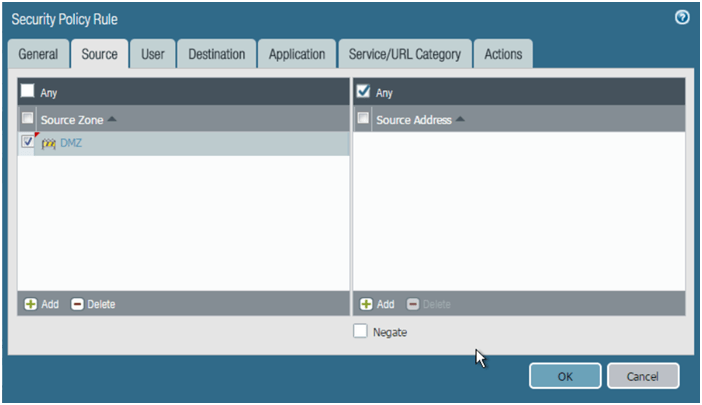
Now go to Security policy and create security policy for the NAT rule.
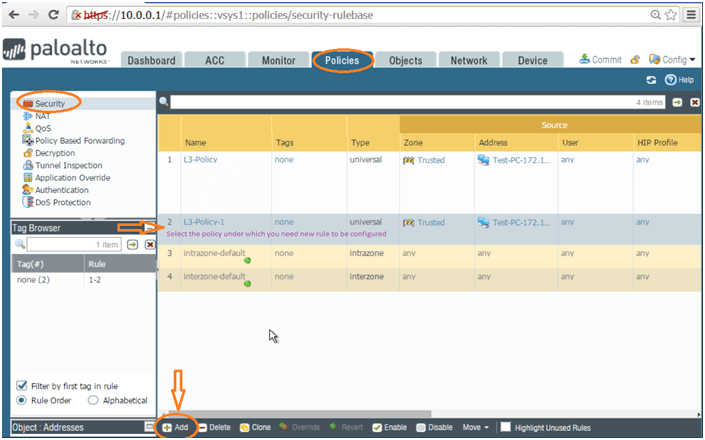
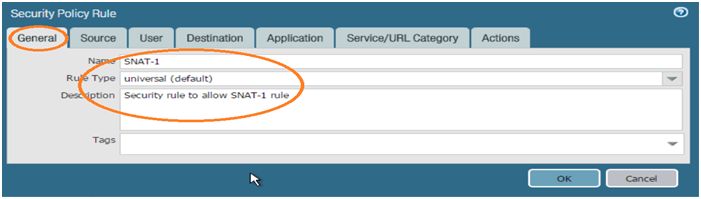
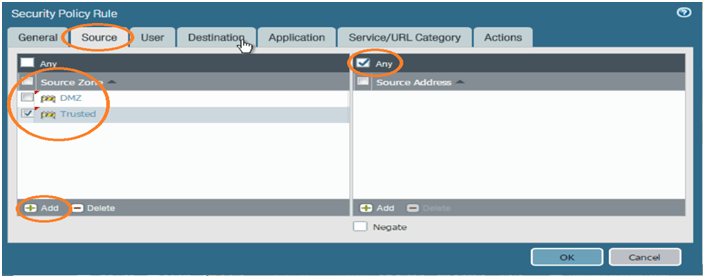
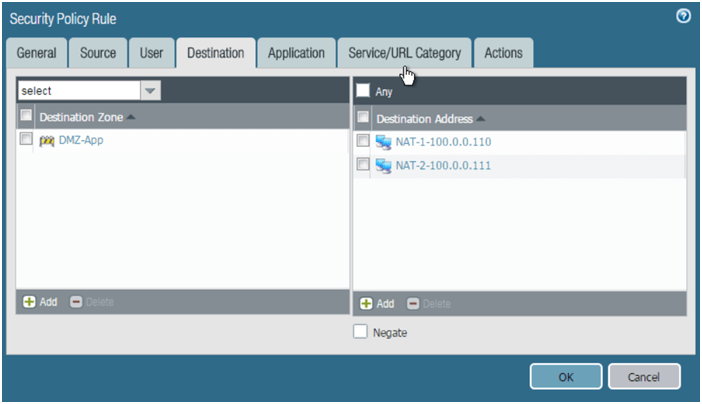
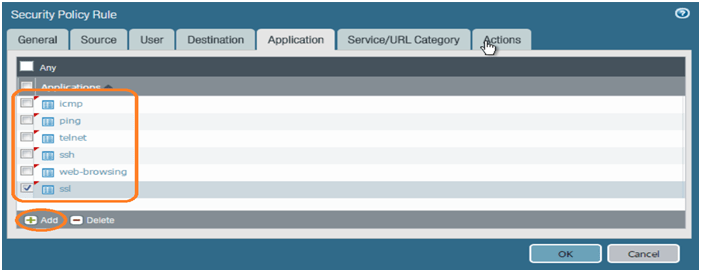
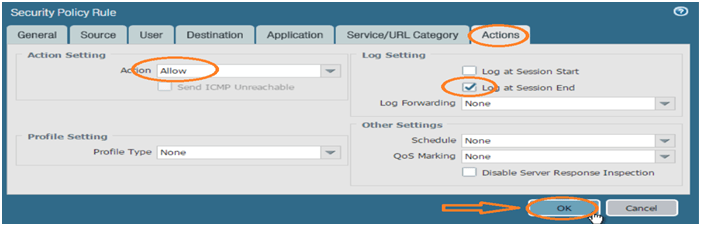
Below is the security policy you configured, which is against number 3. Please refer below screen shot for reference. As the security policy and other configuration is in place, we are good to commit the configuration.
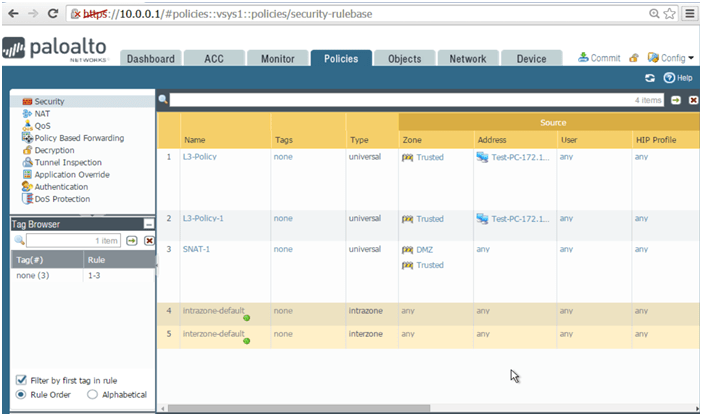
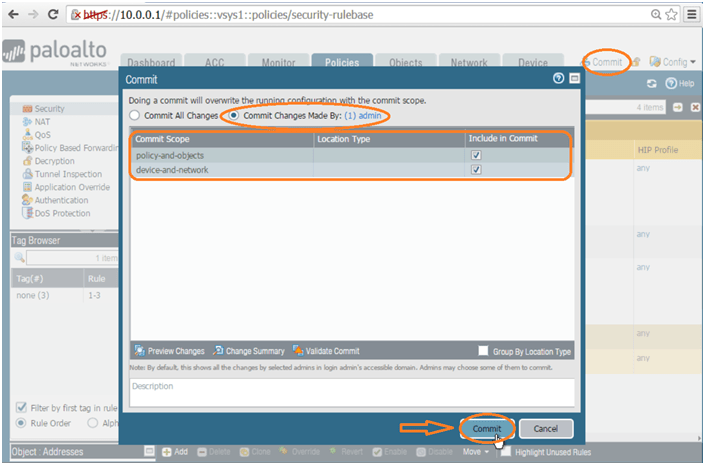
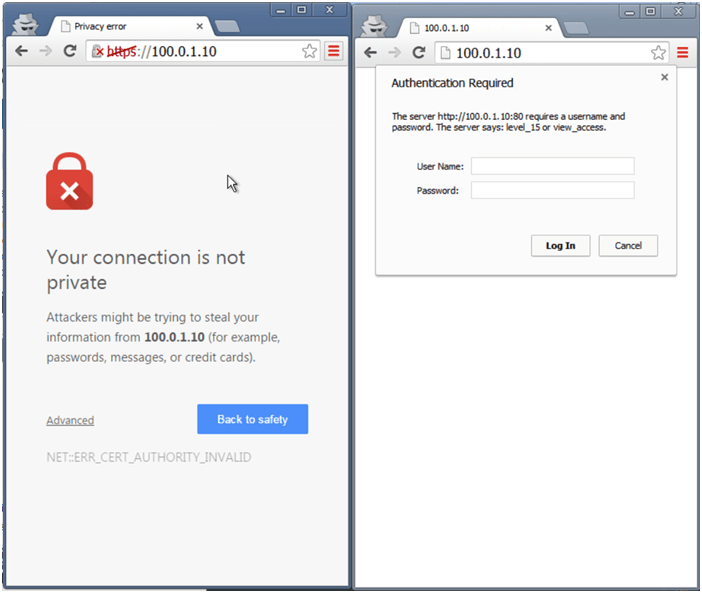
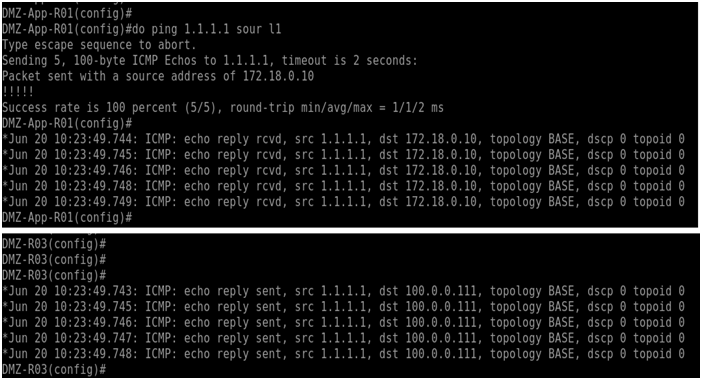
Verify your result for case 1, it should be like below successful result. Try Telnet, SSH and HTTPs by yourself for same IP address.
Case-1 completed.
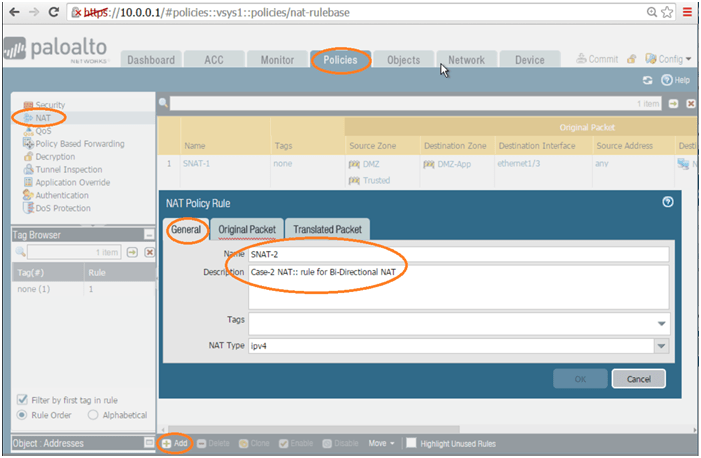
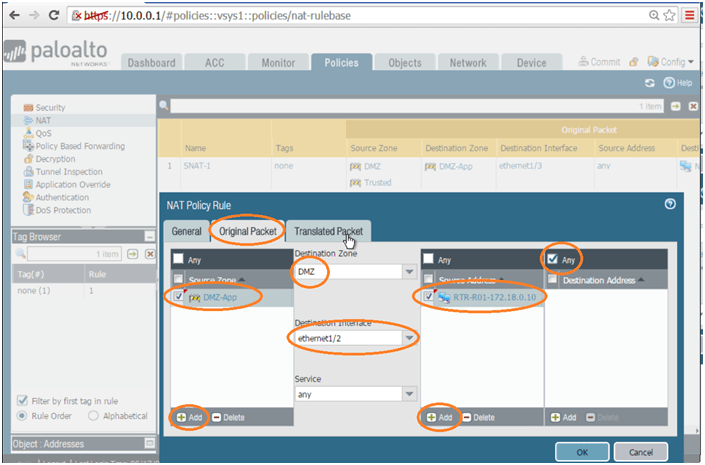
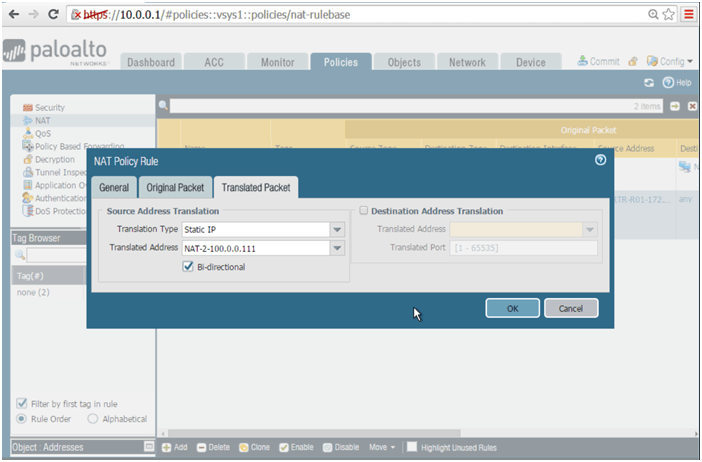
Case-2: Create NAT rule for Bi-Directional NAT. Below are the configuration:
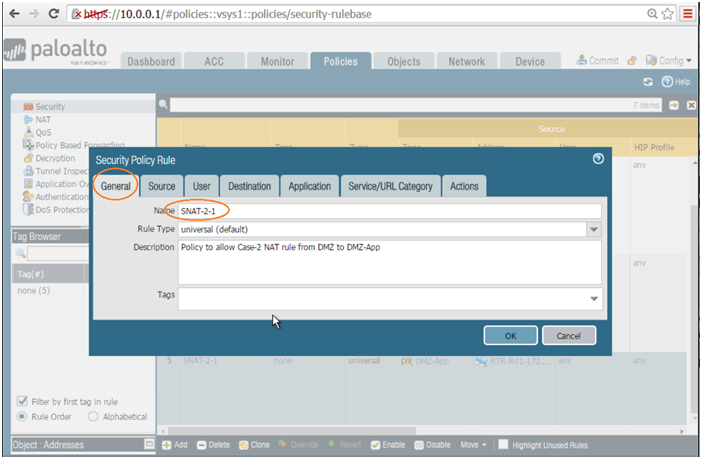
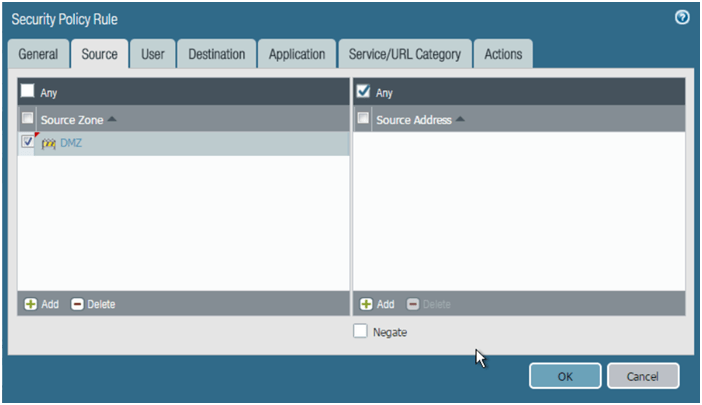
Now let us create the security policies for NAT rules.
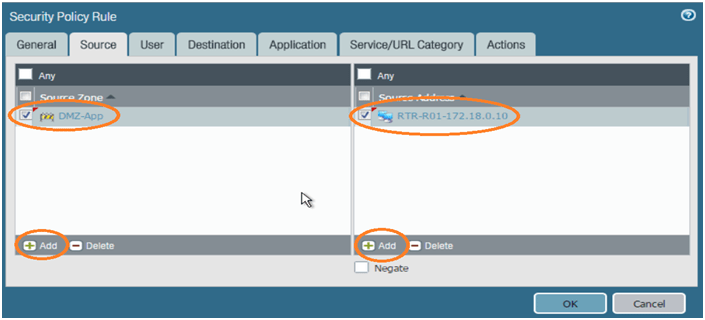
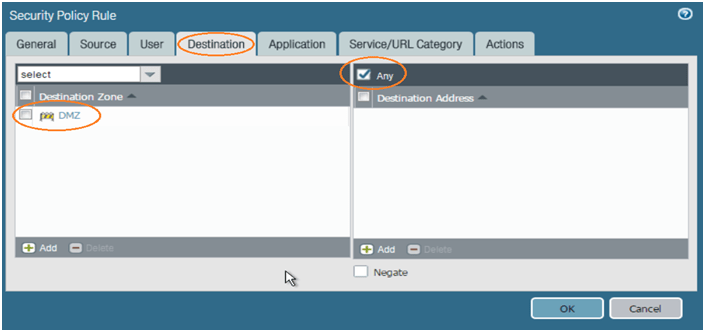
Create one security policy for reverse traffic but destination IP address will be NATed IP address. Easy way, clone SNAT-2 rule and change the values. Refer below:
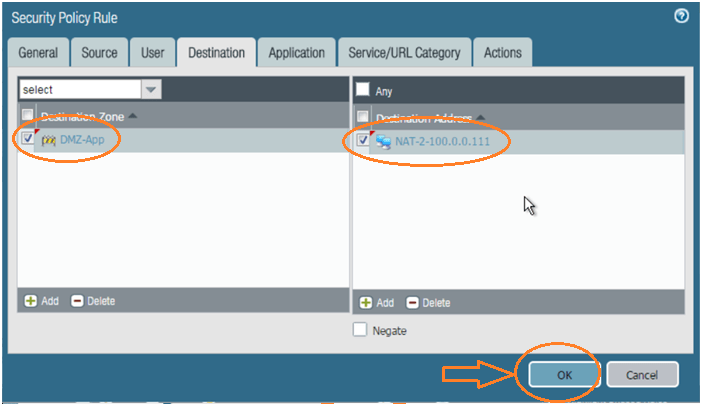
Keep rest of the attributes in the policy as it is and click on OK. Now we are good to proceed with below steps mentioned. Now commit the configuration and verify the result. Below is one test proof.
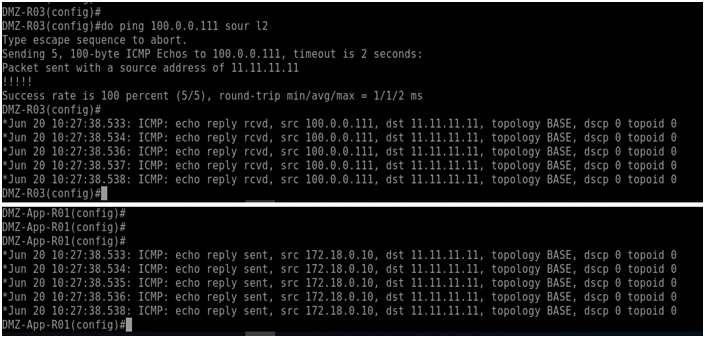
Case-2 Completed.
Comments (0)
Categories
Popular posts
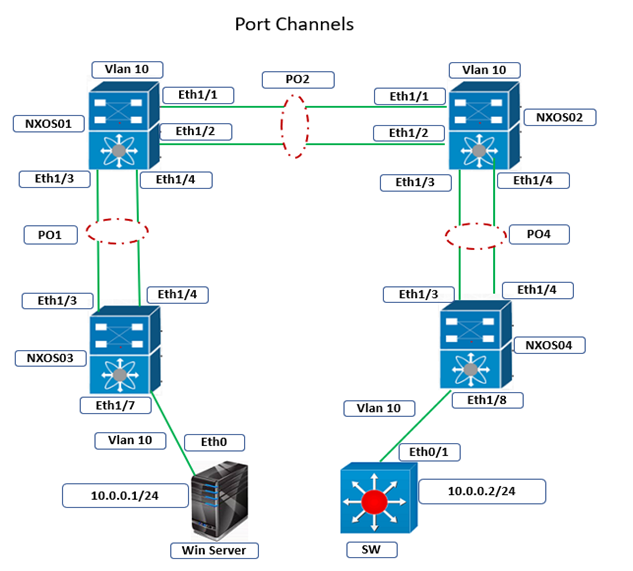
Cisco Nexus Port Channel: Configuring ...
24 Apr 2024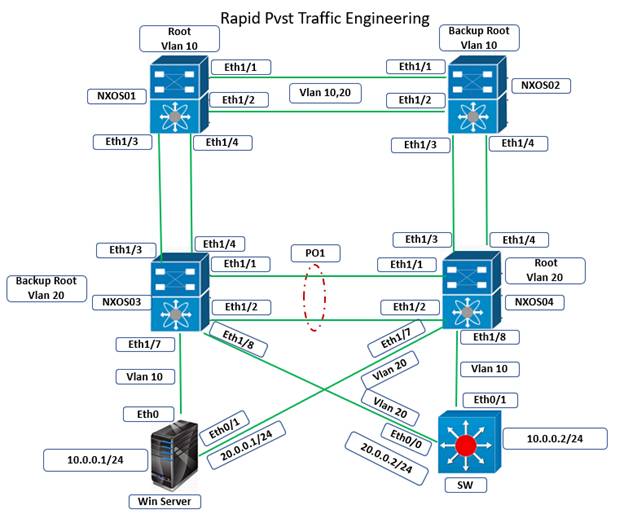
Configure Rapid PVST on Cisco Nexus
5 Apr 2024
Palo Alto Exam Cost: PCNSA, PCNSE & More
28 Mar 2024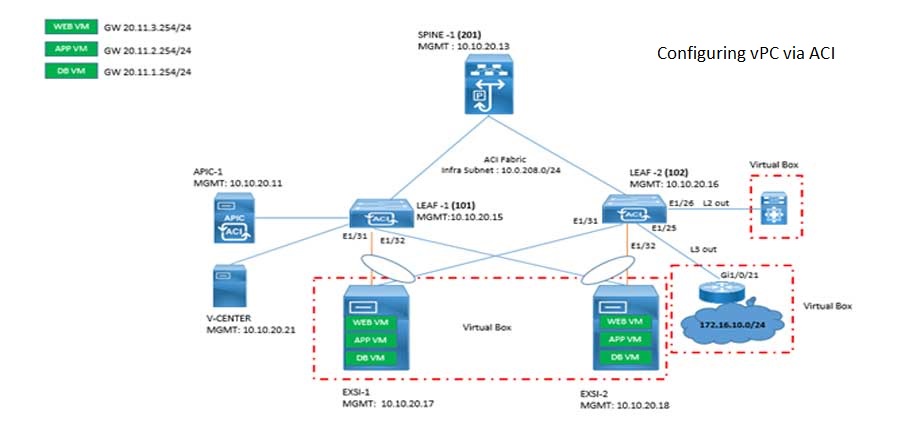
Cisco ACI VPC Configuration Task Steps
6 Jan 2024Recent posts
Types of Network Topology: Explained
25 Apr 2024
AWS Certification Path: Amazon Cloud
25 Apr 2024
Network Hardware Devices: Explained
24 Apr 2024
Palo Alto Firewall Certification ...
24 Apr 2024