Task
● Overview of site to site VPN
● Configure new security gateway with hostname of Branch-firewall and give a ip address of 172.11.5.1 and set a ip address of eth 1 interface is 172.11.6.1 and integration with SM
● Create vpn tunnel both firewalls with secret key authentication and use vpn communities as star type and peer ip would be for dc-SG is 172.11.2.1 and for Branch_SG is 172.11.6.1 and interesting traffic would be same
Explanation
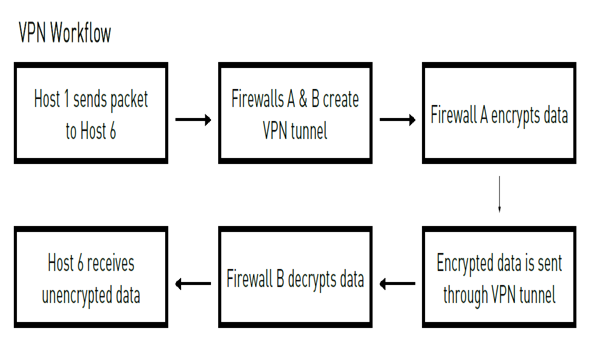
ipsec vpn software blade is used for encrypt and decrypt traffic to and from external networks and client use smart Dashboard to easily configure VPN connections between security gateways and remote devices the vpn tunnel guarantees
Authentication :- Uses standard authentication method like pre shared and certificate based
Privacy : – all vpn data is encrypted
Integrity :- uses industry- standard integrity assurance methods
IKE and IPsec
Check point VPN solution uses these secure VPN protocols to manage encryption keys , and send encrypted packets IKE (internate key EXchange) is a standard key management protocol that is used to create the vpn tunnels ipsec is protocol that supports secure ip communication that are authenticated and encrypted on private or public networks
Site to Site VPN :-
The basis of site to site VPN is the encrypted VPN tunnel . Two security gateways negotiate a link and create a VPN tunnel and each tunnel can contain more than one VPN connections One security gateways can maintain more than one VPN tunnel at the same time.
VPN Communities :- A VPNdomain is a collection ofinternal networks that use security Gateways to send and receive Its a collection of VPN tunnels and their attributes Network resources of different VPN Domains can securely communicate with each other through VPN tunnels that terminate at the security gateways in the VPN communities vpn communities are based on star and mesh topology . in mesh community , there are vpn tunnels b/w each pair of security gateways
Routing VPN traffic :- configure the security gateways to route VPN traffic based on VPN domains or based on the routing settings of the operating system
For each VPN gateway . you must configure an existing gateway as a default gateway
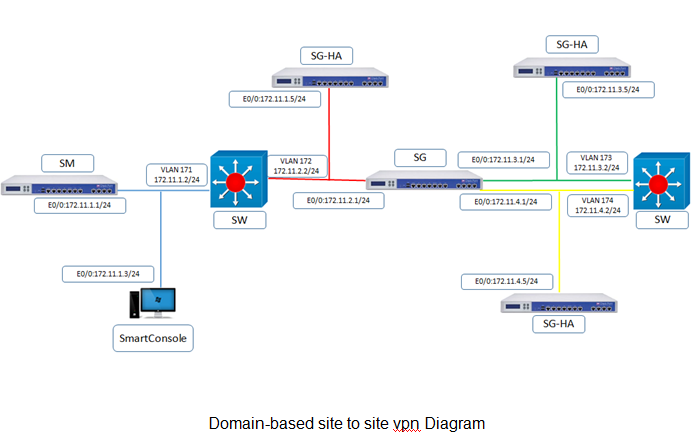
Domain based VPN :- The vpn traffic is routed according to the VPN domain based routing to let satellite security gateways send VPN traffic to each other the center security gateway creates VPN tunnels to each satellite and the traffic is routed to the correct VPN domain
Routed based VPN :- VPN traffic is routed according to the routing setting (static or dynamic) of the security gateway operating system the security gateway uses a VTI (VPN Tunnel Interface) to second the VPN traffic as if it were a physical interface the VTI of Security gateways in a VPN community connect and can support dynamic routing protocols
Configuration
Now we have take GUI of SG from management interface ip-address with username-admin and uninets@123 and open any browser and type https://172.11.5.1 and put credential
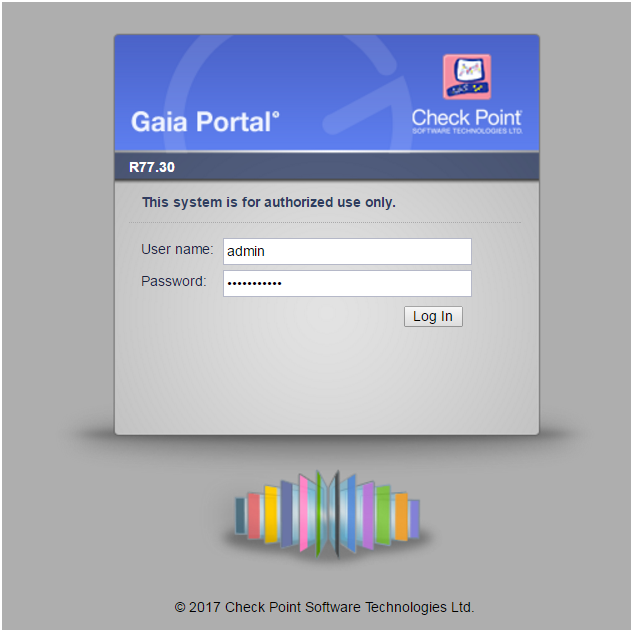
and click on login

and we have click on next
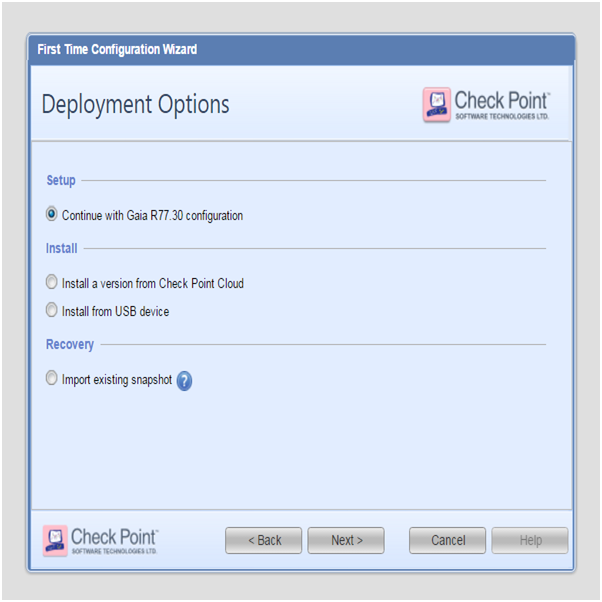
and we will choose first option and click on next
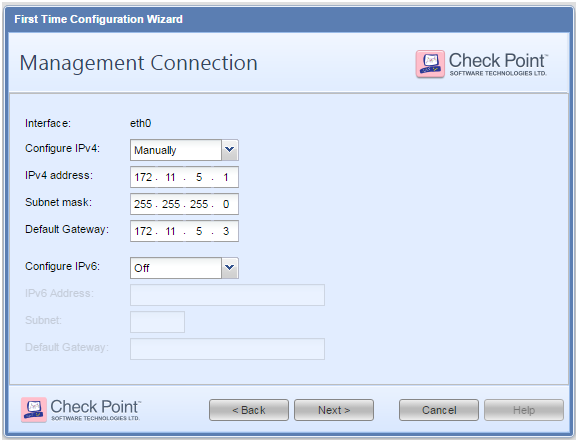
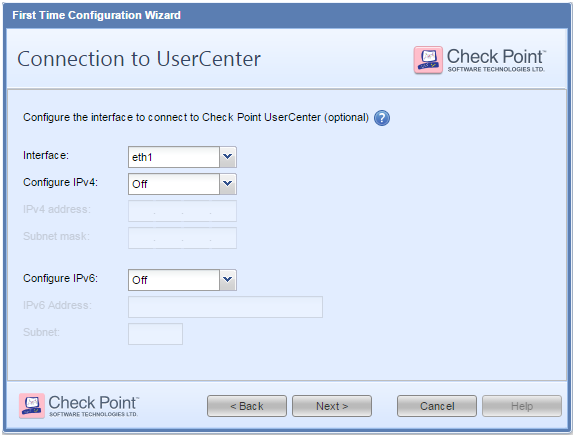
here if we want change IP-address of interface and we can also provide default -gateway and click to next
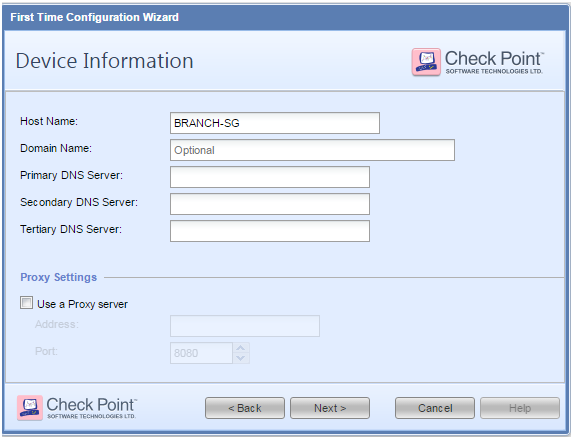
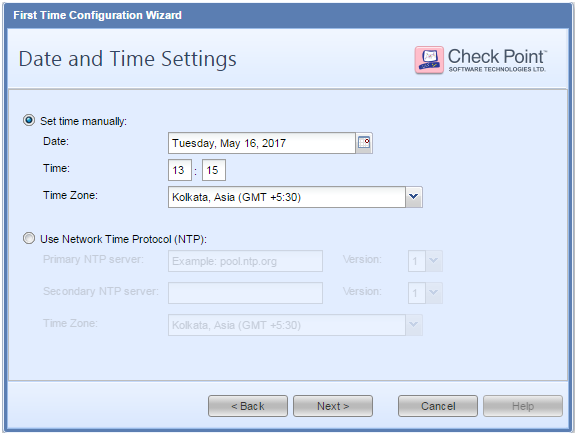
Here we can change the hostname and give domain-name and primary DNS and secondary DNS all details are optional so we not configuring it now we will configure it according to need here we to configure time zone and time for device we have two methods one is manual and another is through NTP but here we don’t have any NTP server so we selected manual method and click on next
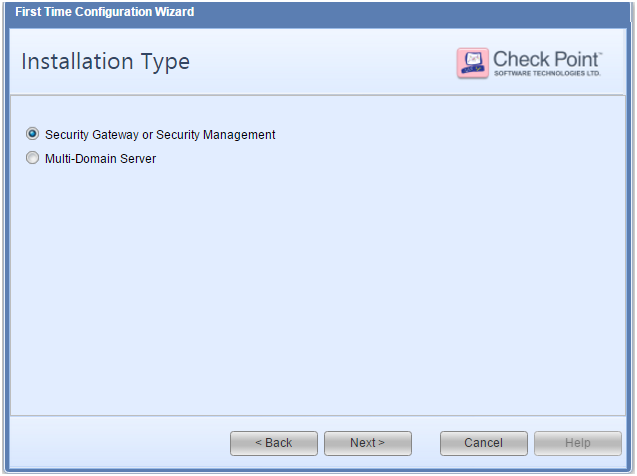
Here we are configuring our IOS working we two options one is for act as a security gateway or security management and one is multi-domain server and its use for manage multiple security managements but we have one security management we will choose first and click on next
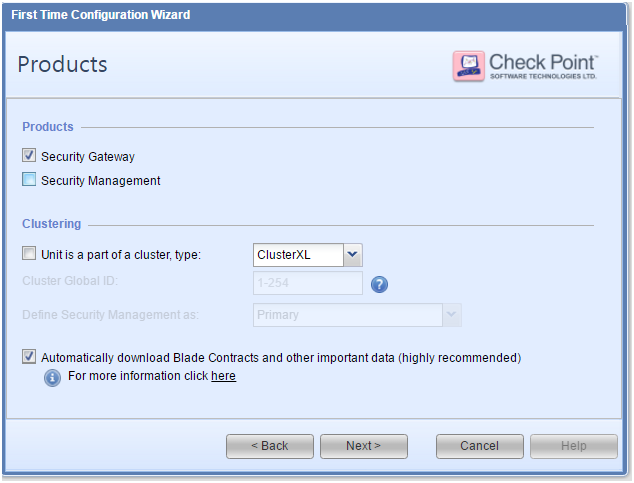
So here we are operating devices in distributed mode (As we discussed earlier ) so we will select Security-Gateway and click on next
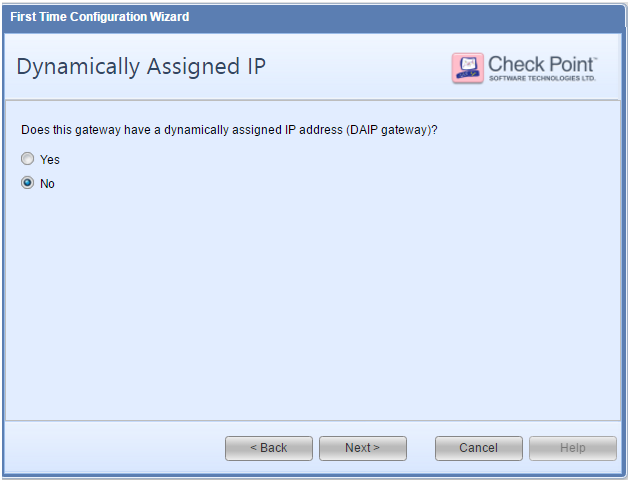
Here its asking for ip-gateway assignment to firewall from Dhcp but already give manual so selected NO
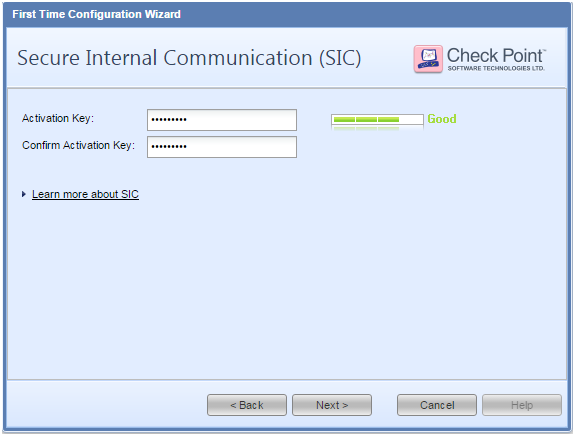
here giving password for SIC Process so SM can authenticate SG
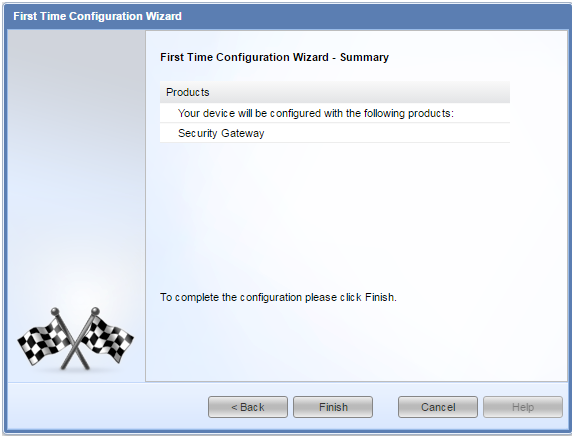
click on Finish IF configured properly then its our final view
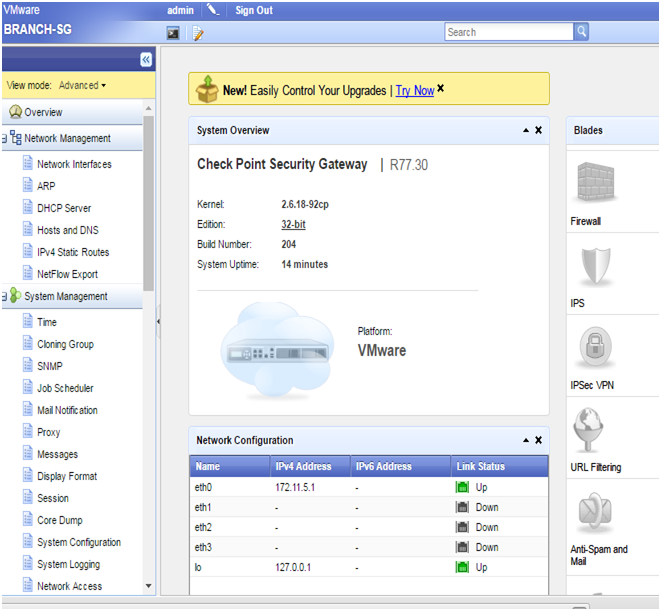
Now we to set ip address on interface eth1 so login into Branch_SG and enter login credential is username- admin password-uninets@123
BRANCH-SG>
BRANCH-SG> set interface eth1 ipv4-address 172.11.6.1 subnet-mask255.255.255.0
BRANCH-SG> set interface eth1 state on
BRANCH-SG> show interface eth1
state on
mac-addr 50:13:00:04:00:01
type ethernet
link-state link up
mtu 1500
ipv4-address 172.11.6.1/24
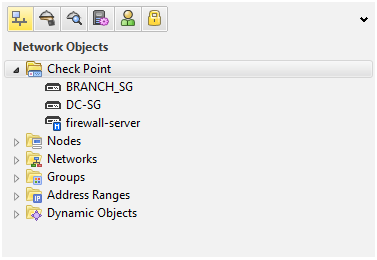
here we can see that we gave ip address to interface eth1 and now we have login into smart dashboard and add new security gateway like we added before
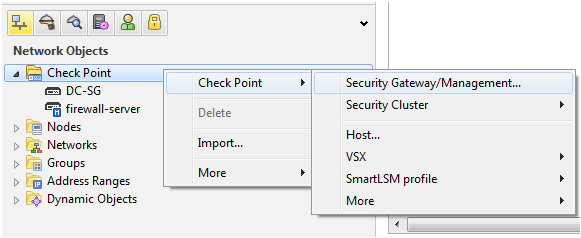
here we are going to add new security gateway on security manager
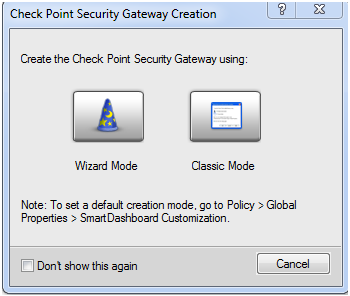
no click on click mode
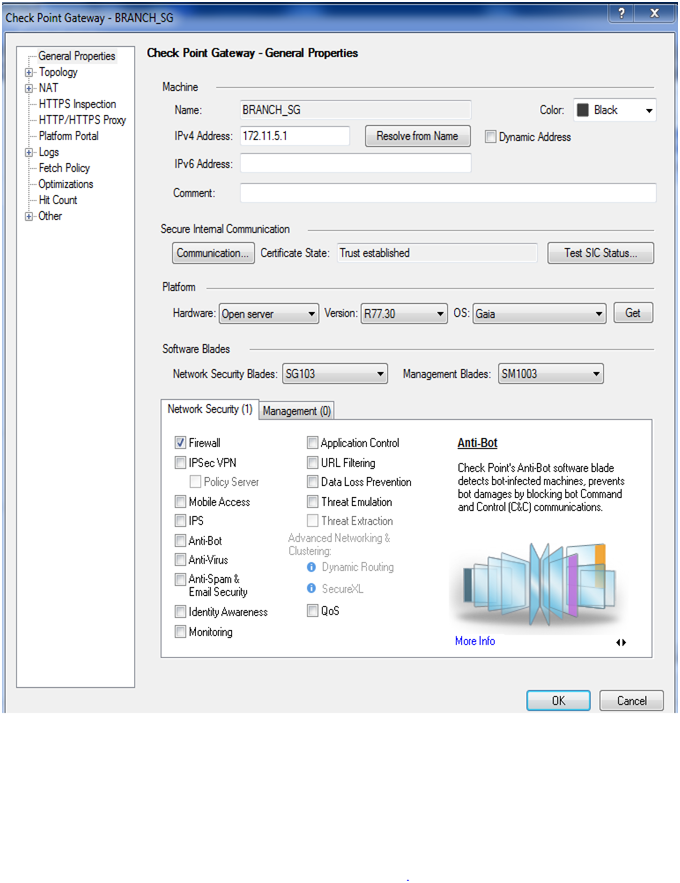
here we need to mention firewall name and their ip address and click on communication tab put sic process password and initialized it then click on ok here we can see that Branch- SG has been added on Sm
Now we have to enable VPN blades on both firewalls
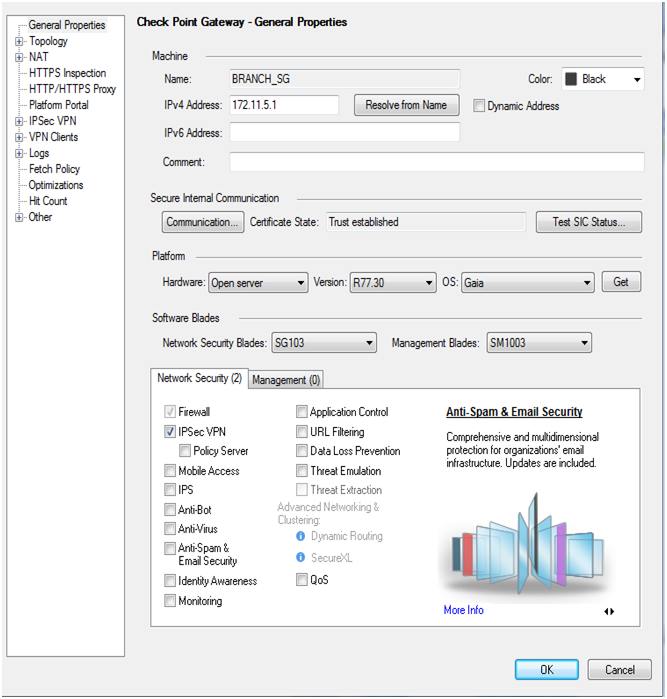
So check mark on IPSec VPN blade then click on ok enable on next firewall

Now we enabled ipsec blade on DC-SG Now we have to define vpn communities to define VPN peers and other VPN attributes then click on vpn communities and select site to site VPN
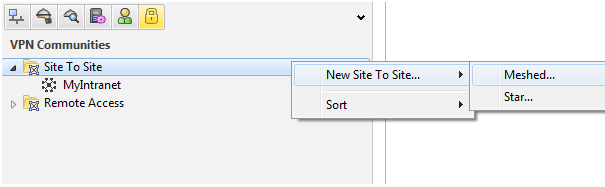
Click on new site to site and select topology type meshed because we have just two firewalls
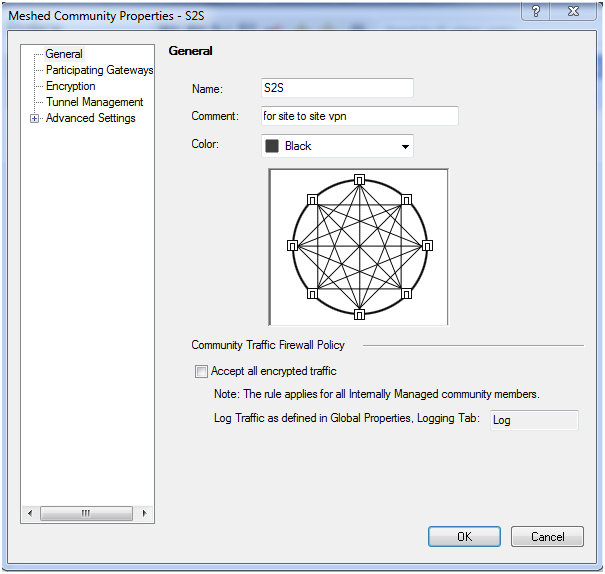
give to any name we gave S2S then click on participating gateways tab
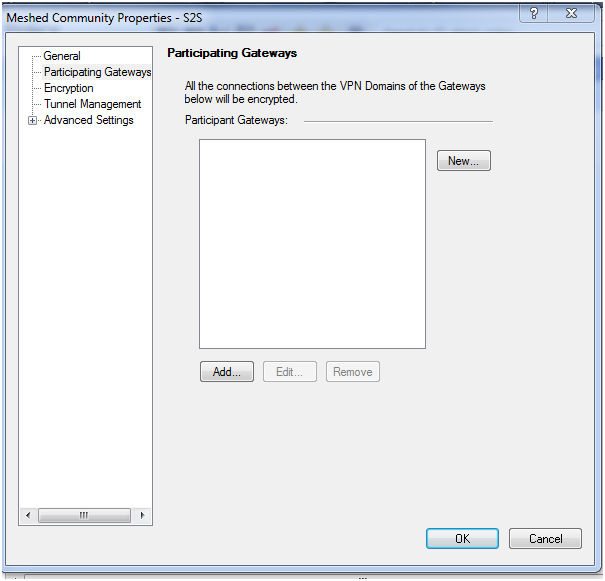
click on add
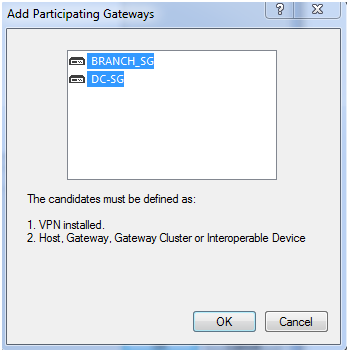
Click on ok here adding both firewall then click on encryption tab
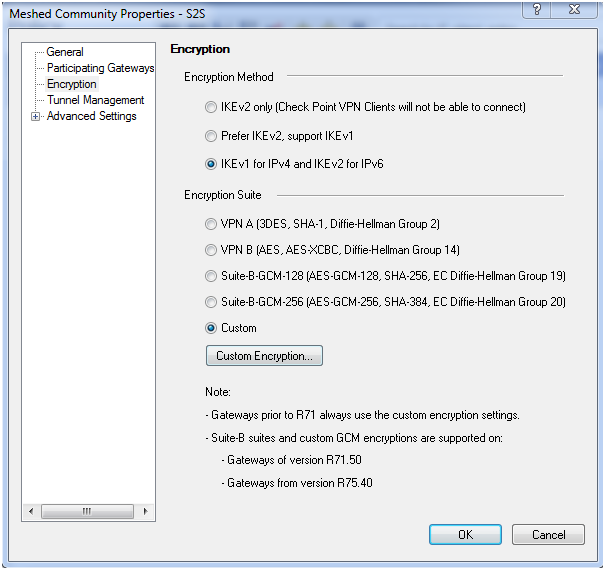
We choose default but we want use customize configuration then select custom then select methods from there then click on then click on advance setting tab
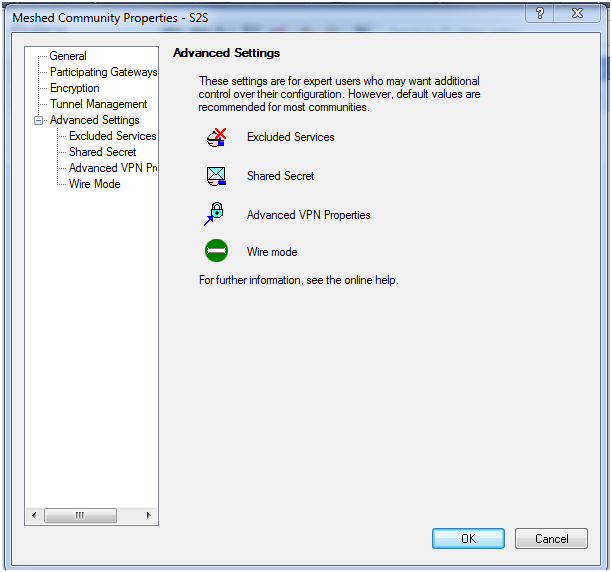
Here we don't need to change anything then click on ok
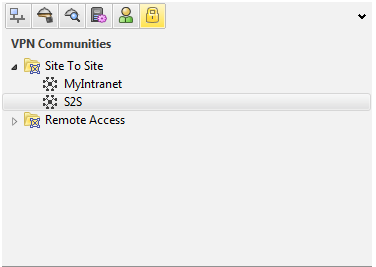
Here we can see that S2S communities has been created Now we have to define rule base for vpn so click on policy tab
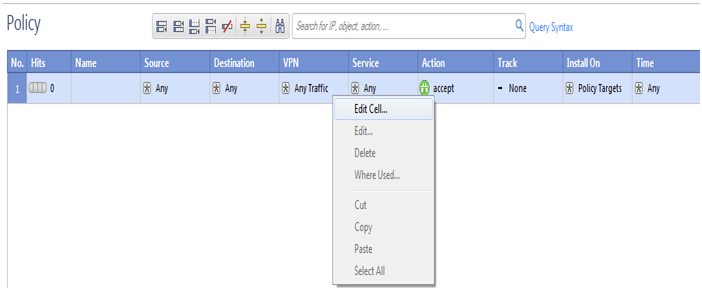
We are not mention any source or destination now we have to add communities so click on VPN tab and click on edit cell
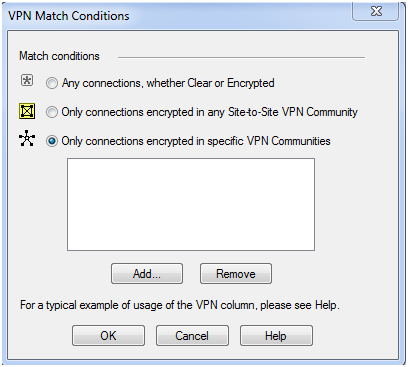
Here we select third option and click on add
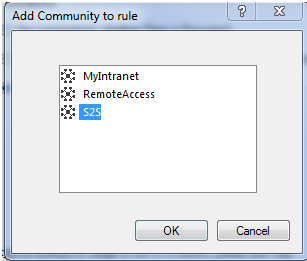
Here we are choosing our created communities S2S click on ok
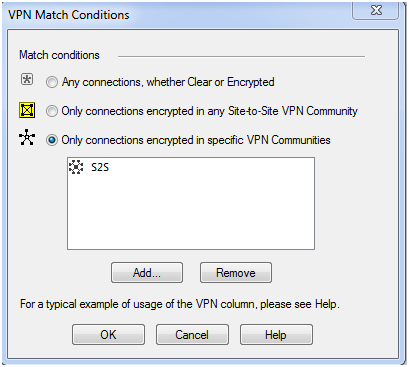
click on ok here also
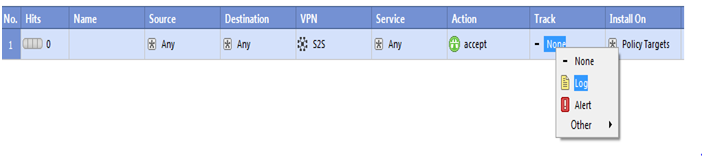
we want track it so click on track and select log click on ok and save the policy then push the policy
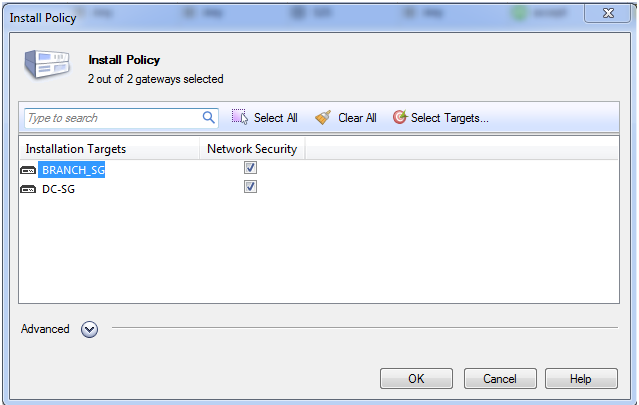
we selected both security gateways to push policies so now click on ok
Verification :-
BRANCH-SG> ping 172.11.2.1
PING 172.11.2.1 (172.11.2.1) 56(84) bytes of data.
64 bytes from 172.11.2.1: icmp_seq=5 ttl=64 time=1.06 ms
64 bytes from 172.11.2.1: icmp_seq=6 ttl=64 time=0.924 ms
64 bytes from 172.11.2.1: icmp_seq=7 ttl=64 time=1.00ms
Now we have to verify through smart view tracker
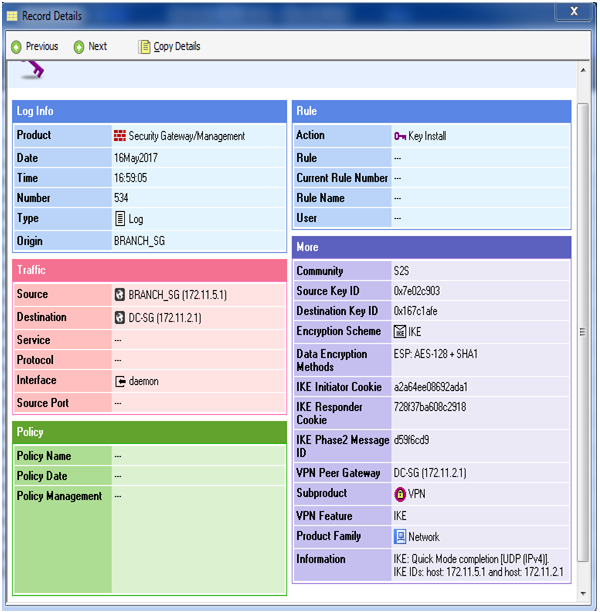
Here we can check tunnel has been created here source is Branch-SG and destination is DC-SG and all traffic has been encrypted Now we can verify through cmd so logon into Branch-SG
BRANCH-SG> expert
Enter expert password:
Warning! All configuration should be done through clash You are in expert mode now.
[Expert@BRANCH-SG:0]# vpn tu
********** Select Option **********
(1) List all IKE SAs
(2) List all IPsec SAs
(3) List all IKE SAs for a given peer (GW) or user (Client)
(4) List all IPsec SAs for a given peer (GW) or user (Client)
(5) Delete all IPsec SAs for a given peer (GW)
(6) Delete all IPsec SAs for a given User (Client)
(7) Delete all IPsec+IKE SAs for a given peer (GW)
(8) Delete all IPsec+IKE SAs for a given User (Client)
(9) Delete all IPsec SAs for ALL peers and users
(0) Delete all IPsec+IKE SAs for ALL peers and users
(Q) Quit
1
Peer 172.11.2.1 SAs:
- IKE SA :
[Expert@BRANCH-SG:0]# vpn tu
********** Select Option **********
(1) List all IKE SAs
(2) List all IPsec SAs
(3) List all IKE SAs for a given peer (GW) or user (Client)
(4) List all IPsec SAs for a given peer (GW) or user (Client)
(5) Delete all IPsec SAs for a given peer (GW)
(6) Delete all IPsec SAs for a given User (Client)
(7) Delete all IPsec+IKE SAs for a given peer (GW)
(8) Delete all IPsec+IKE SAs for a given User (Client)
(9) Delete all IPsec SAs for ALL peers and users
(0) Delete all IPsec+IKE SAs for ALL peers and users
(Q) Quit
Peer 172.11.2.1 SAs:
- SPI’s related to IKE SA :
INBOUND:
- 0x7e02c903
OUTBOUND:
- 0x167c1afe
Same thing we can check on DC-SG so login into DC-SG and verify all SA for phase-1 and PHASE-2 SA (ipsec-sa)
Enter expert password:
Warning! All configuration should be done through clish
You are in expert mode now.
[Expert@firewall-Gateway:0]# vpn tu
********** Select Option **********
(1) List all IKE SAs
(2) List all IPsec SAs
(3) List all IKE SAs for a given peer (GW) or user (Client)
(4) List all IPsec SAs for a given peer (GW) or user (Client)
(5) Delete all IPsec SAs for a given peer (GW)
(6) Delete all IPsec SAs for a given User (Client)
(7) Delete all IPsec+IKE SAs for a given peer (GW)
(8) Delete all IPsec+IKE SAs for a given User (Client)
(9) Delete all IPsec SAs for ALL peers and users
(0) Delete all IPsec+IKE SAs for ALL peers and users
(Q) Quit
*******************************************
1
Peer 172.11.5.1 SAs:
- IKE SA :
Hit key to continue …
********** Select Option **********
(1) List all IKE SAs
(2) List all IPsec SAs
(3) List all IKE SAs for a given peer (GW) or user (Client)
(4) List all IPsec SAs for a given peer (GW) or user (Client)
(5) Delete all IPsec SAs for a given peer (GW)
(6) Delete all IPsec SAs for a given User (Client)
(7) Delete all IPsec+IKE SAs for a given peer (GW)
(8) Delete all IPsec+IKE SAs for a given User (Client)
(9) Delete all IPsec SAs for ALL peers and users
(0) Delete all IPsec+IKE SAs for ALL peers and users
(Q) Quit
Peer 172.11.5.1 SAs:
- SPI’s related to IKE SA :
INBOUND 1. 0x167c1afe
OUTBOUND: 1. 0x7e02c903
here we verify that Phase-1 and phase-2 has been created and data is encrypting and decrypting on both sides
Comments (0)
Categories
Popular posts
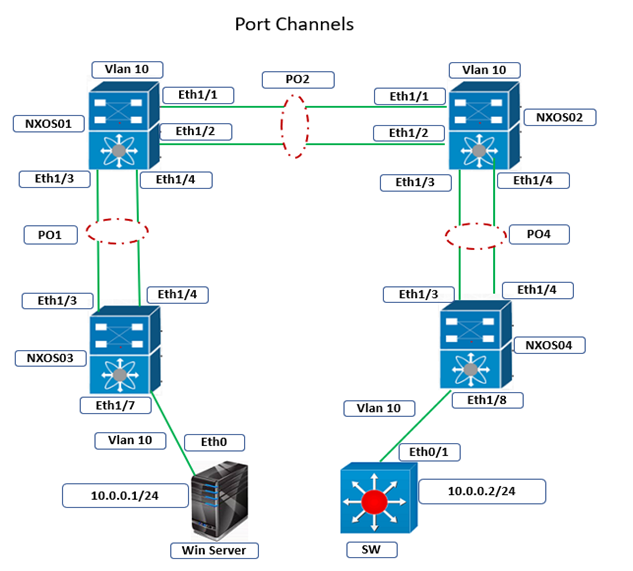
Cisco Nexus Port Channel: Configuring ...
4 Apr 2024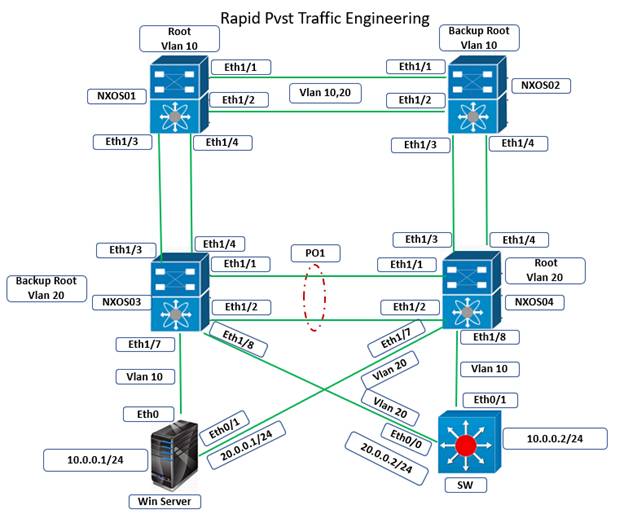
Configure Rapid PVST on Cisco Nexus
5 Apr 2024
Palo Alto Exam Cost: PCNSA, PCNSE & More
28 Mar 2024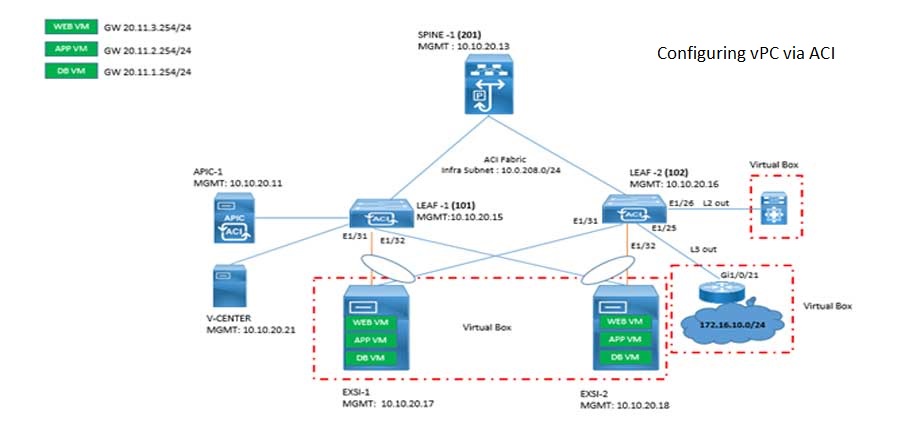
Cisco ACI VPC Configuration Task Steps
6 Jan 2024Recent posts

AWS Certification Path: Amazon Cloud
18 Apr 2024
SD-WAN Vendors Comparison: Choosing the ...
16 Apr 2024
CCNP Certification Cost and Exam Fees
12 Apr 2024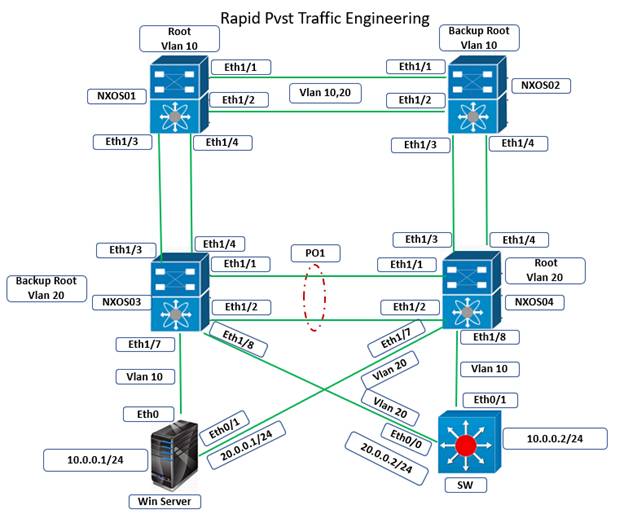
Configure Rapid PVST on Cisco Nexus
5 Apr 2024




