
This Troubleshooting 802.1x document provides the step-by-step procedures that are documented for easy reference and later use for the 802.1X Basic Troubleshooting. The IEEE 802.1X standard defines a client-server-based access control and authentication protocol that restricts unauthorized devices from connecting to a LAN through publicly accessible ports. The authentication server authenticates each client connected to a switch port before making available any services offered by the switch or the LAN.
Until the client is authenticated, 802.
1X access control allows only Extensible Authentication Protocol over LAN (EAPOL) traffic through the port to which the client is connected. After authentication is successful, normal traffic can pass through the port.
This enables establishing best practices for commonly performed procedures and aids in introducing consistency in processes and hence an enhancement in service levels.
In locations where we do not control the cabling we need to use 802.1x to take care of the security. It is decided to implement 802.
1x on the local switch since Statoil is not responsible for the cabling/infrastructure. All Laptops and printers connected to the switch have to be authorized to the Radius/AD with their certificate to get an open/authorized port on the switch. When they are authorized a normal logon procedure is required to access applications.
Use the following CLI commands to troubleshoot AAA issues:
• show aaa authentication
• show radius status
• show radius-server
• Show aaa server
Use the following debug commands to determine the root cause of an issue:
• debug radius aaa-request
• debug radius aaa-request-low-level
• debug dot1x errors/events
• debug radius brief/retransmit
When configuring a switch port with 802.1x. Should have the below standard configuration included :-
• authentication event server dead action authorize
• authentication event server alive action reinitialize
• authentication port-control auto
• authentication timer reauthenticate 100
• authentication violation protect
• dot1x pae authenticator
When configuring a switch with 802.1x. Configuration to verify :-
• aaa authentication dot1x default group radius
• ip radius source-interface Vlan Management
• dot1x system-auth-control
• dot1x critical eapol
• radius-server source-ports extended
• radius-server host 10.217.105.245 auth-port 1812 acct-port 1813
• radius-server host 10.217.105.246 auth-port 1812 acct-port 1813
• radius-server key 7 1046080B01161C0C09163C22202C32
• radius-server deadtime 1
• radius-server dead-criteria time 10 tries 2
Comments (0)
Categories
Popular posts
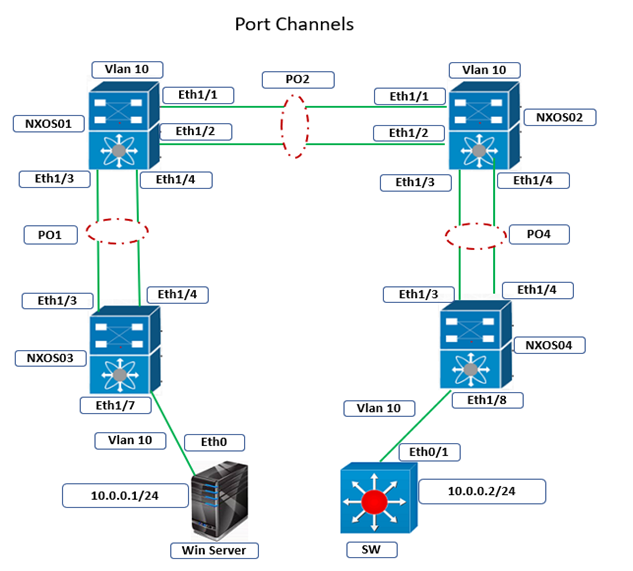
Cisco Nexus Port Channel: Configuring ...
4 Apr 2024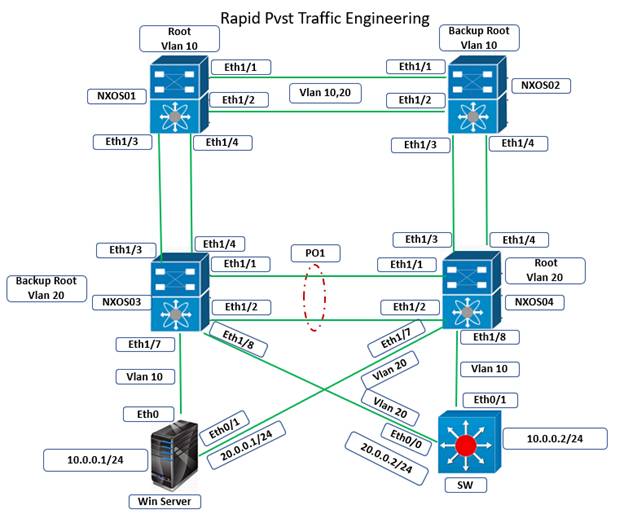
Configure Rapid PVST on Cisco Nexus
5 Apr 2024
Palo Alto Exam Cost: PCNSA, PCNSE & More
28 Mar 2024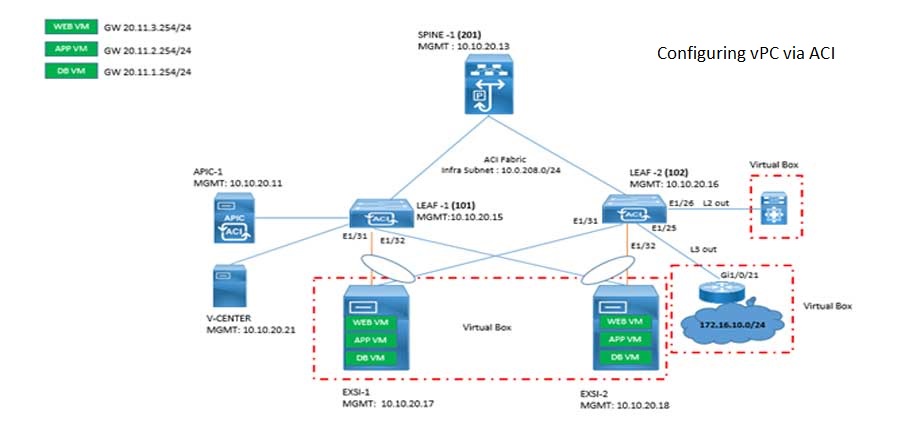
Cisco ACI VPC Configuration Task Steps
6 Jan 2024Recent posts

AWS Certification Path: Amazon Cloud
18 Apr 2024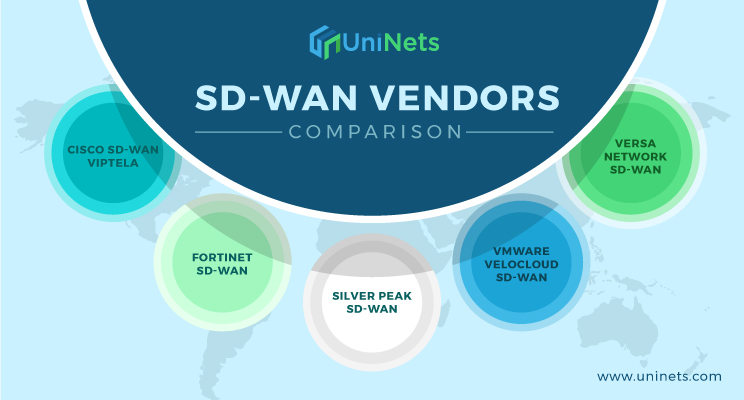
SD-WAN Vendors Comparison: Choosing the ...
16 Apr 2024
CCNP Certification Cost and Exam Fees
12 Apr 2024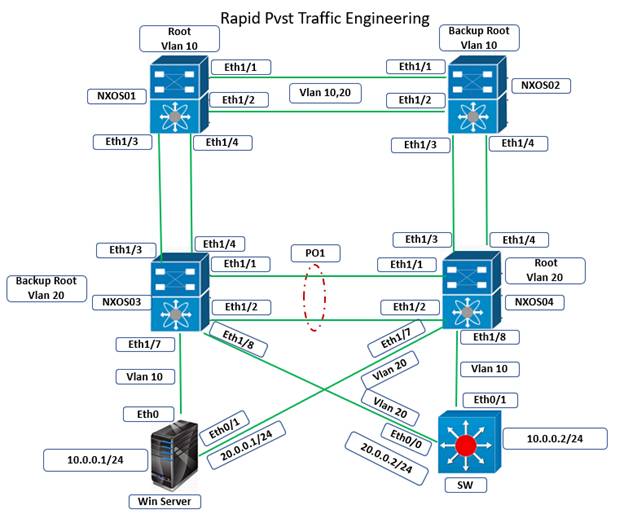
Configure Rapid PVST on Cisco Nexus
5 Apr 2024




